If you are a new student of White Hat hacking or Ethical Hacking course then you must have heard the term of Honeypot, which is used to lure the potential cyber attackers into a trap. Also, all the White hackers and Ethical hacking experts use the Kali Linux OS as their main OS cum tool to deal with cyber-attacks and to commit any White hat cyber-attack.
Who needs to set Cyber Honeypot? Learn to Setup Honeypot
Now whether you are a student of Ethical hacking or a professional white-hat hacker, you must learn how to setup Honeypots to lure away the potential attacker to protect your targeted system or website or server. Also, if you have just started hacking or cybersecurity learning this trick will clear the Honeypot on Kali Linux concept while increasing knowledge.
Facts about Honeypots
- Most of the cyber-security experts do depend on the Honeypot setup, as the first protection against the hackers.
- The use and the mechanism of Honeypot is quite simple, as these setups are put in place to mimic any targeted or particular website, system or data archives for the cyber-attackers. With putting the honeypot in place, admins not only can detect and log attacks to certain services also can register the originating IP address of related attack, hence protecting the system and detecting the criminal both are done at the same place.
- You may think off all the Hacking related techniques involve a lot of coding and demands huge expertise over the topic, while setting up a Honeypot is very simple and if you have already installed Kali Linux on your PC then it is just matter of minutes.
In this article I am going to show you how using the combination of Kali Linux and Pentbox, anyone can have a Honeypot set up, ready to go in minutes.
Honeypot Perquisites
- A PC where Kali Linux is installed and you will need the admin rights in that PC as well.
- Also, you will be needing an application called Pentbox which you have to download and install through the command-line interface, to use admin-level privileges.
How to download and start Pentbox
- Type the below in the terminal command-line interface.
wget http://downloads.sourceforge.net/project/pentbox18realised/pentbox-1.8.tar.gz
- Once the file download is finished, extract the files from the downloaded archive, which is
tar xvfz pentbox-1.8.tar.gz
- By doing the above step you will have a new directory (folder) named pentbox-1.8. Now go to that directory from by using the terminal command
cd pentbox-1.8
How to run Pentbox
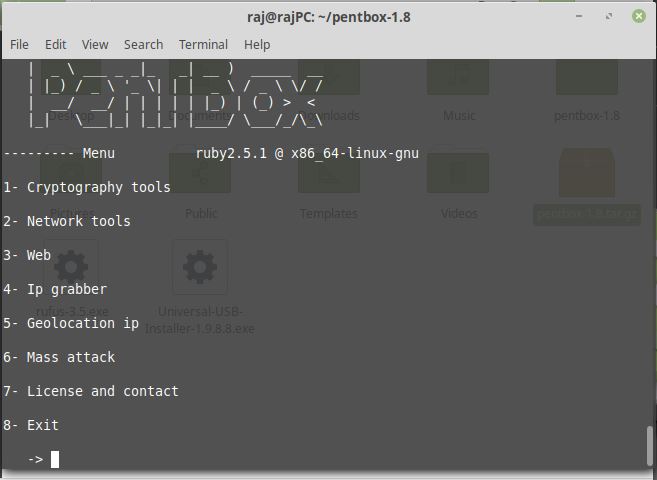
Now run Pentbox Ruby script with this command ./pentbox.rb
Note: If you don’t have ruby then install that first before running the Pentbox script:
sudo apt install ruby
Activate the HoneyPot on your Kali Linux
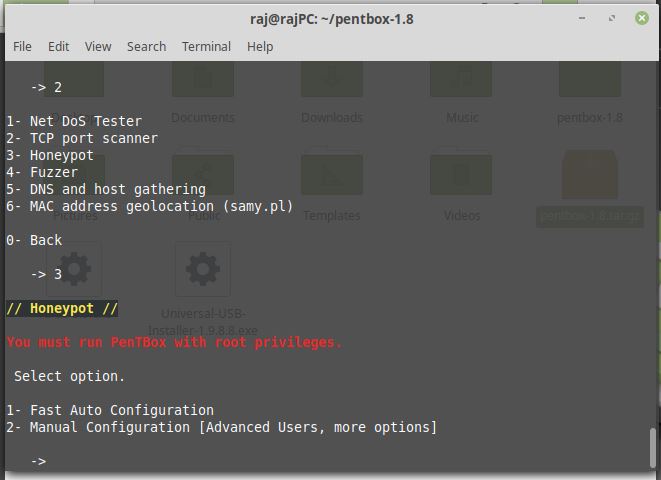
After issuing the command, the user would be greeted by a menu on the terminal window. From that menu, you have to select 2 (for Networking tools) and then select 3 for Honeypot, according to the figure below.
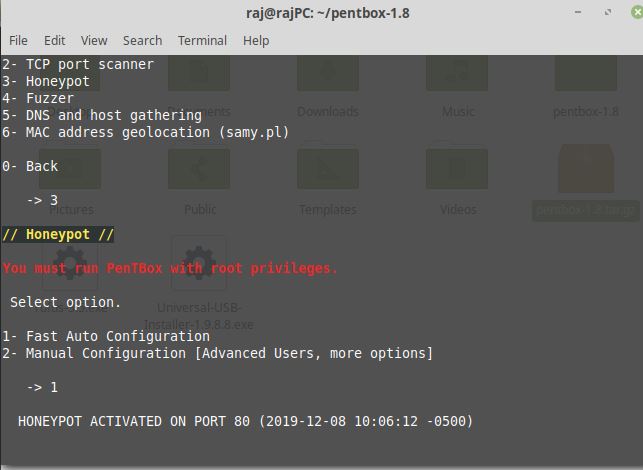
Now you have the next menu, here select 1 (for Fast Auto Configuration) and the honeypot listening on port 80 is launched. Like the image below:
Test Honeypot is working or not
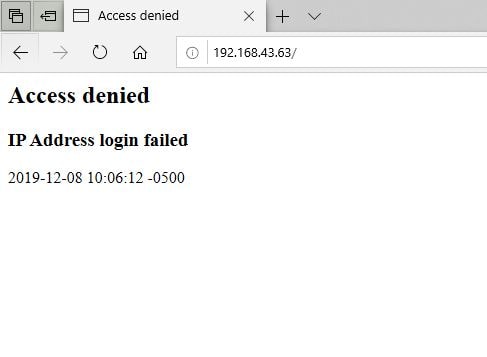
Now you have to open a web browser on another PC (2nd PC or virtual machine must be connected to the same network as the Honeypot you are setting up) and you have to point it towards http://SERVER_IP (where SERVER_IP is the IP address of Honeypot Kali machine). You will be stopped by an “Access Denied” message on the webpage.
Now you have to go back to the Kali Linux terminal window of the Honeypot PC and you would be able to see that the Honeypot picked up the requested connection from the 2nd Consider the below pic.
Honeypot for some specific port number
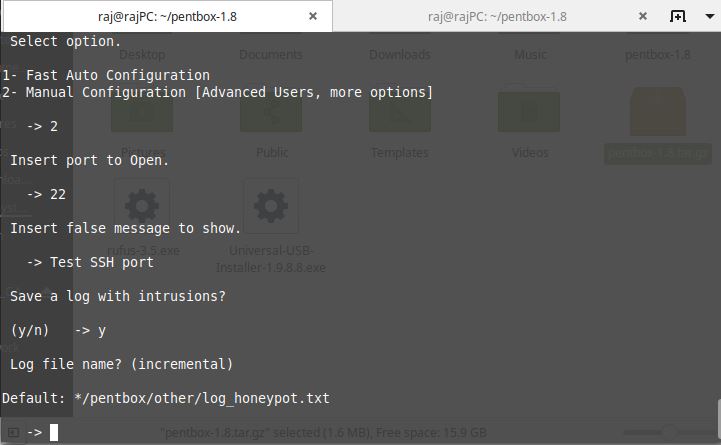
Now to launch any specific instance, we have to launch a Honeypot in manual mode. Let us assume you are facing trouble with cyber-attacks on SSH. Then you have to deploy Pentbox such that it’s would listen to port 22. Thus, to tackle this, stop the running honeypot using ctirl+c and again run the Pentbox script and then again Network Tools->Honeypot and this time instead of selecting Fast Auto configuration mode go for Manual COnfiguration [Advanced Users, more options].
- Insert Port to Open: 22 (You can choose any other port as well)
- Insert false message to show: (Whatever you want) Here we are giving “Test SSh port”
- Save a log with intrusions: Y
- Log filename: Press the Enter button to leave it as default.

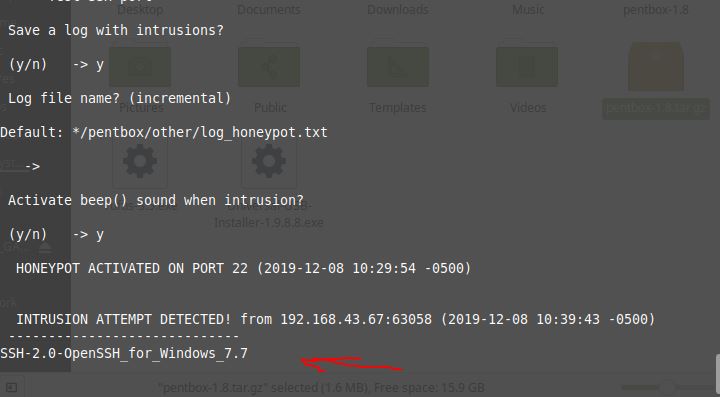
- Activate beep sound when intrusion: Now you can also set up a beep announces for any attempt of intrusion. When the Honeypot is up and running, any attempted breach to SSH into the Kali Linux machine from your 2nd pc or any other pc on the network, you will have the beep and also the log of the attempted actions.

Try to access SSH port of Kali Linux from any other computer, you will get a beep, message of intrusion of command screen as well as details in the log file.
In the above pic, you can see, Pentbox is giving the alert message as well as detecting the originating IP address. Though the attacker may have used some IP address bouncer or masked IP address, the system on Pentbox does its job by reporting the initiator IP address only. In case of a masked IP user, you may have to take other means to detect the attacker. Congratulation, on the deployment of your fist honeypot, you are now one step closer to become a White hat cybersecurity expert.


Related Posts
How to Reopen Closed Windows or Tabs in Firefox
How to Install Django on Windows 11 or 10
How to set Gemini by Google as the default Android assistant
How to create data bars in Microsoft Excel for numeric values
How to open HEIC images on Windows for free
How to install Server Manager Windows 11 or 10