Although Bitcoin has been the most volatile in the past few years, yet this has not deterred the criminals from collecting bits from the Bitcoins. When we talk about extortion, we have seen the emergence and effectiveness of Ransomware using Bitcoins and other forms of crypto-currencies. We have also seen Crypto-Currency Miner (sic.Monero) being deployed on hacked servers/systems, so as to take advantage of the computational resources and generate crypto-currencies. However, lately, we have seen a rising trend in extortion emails, asking for Bitcoins.
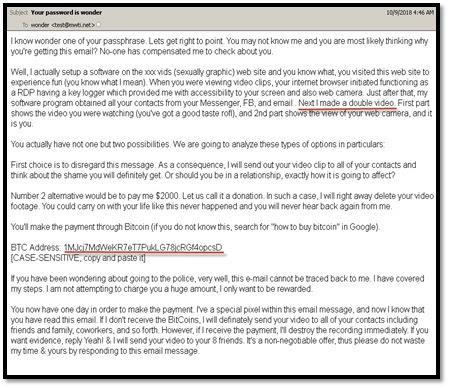
These emails are in plain text format and warn the recipient of a malware being deployed on an Adult Porn Site, furthermore, in the mails, it is also explained in brief how the recipient’s, the webcam was hacked, keylogger was deployed and the login credentials were stolen. The email also explains that a video was captured while they were busy visiting the Adult Porn site and the recipient is threatened with dire consequences viz. sharing of the video with those present in the stolen address book.
Similar to Ransomware and Miner Attacks, this scam also relies on the anonymity provided by crypto-currencies. It’s a simple plain text threat, based on the premise that the recipient has visited some Porn site. The criminals have in most of the cases, successfully invoked the aspect of fear and social stigma into the psych/mind of the email recipients.
eScan’s research team has been analyzing and tracking these emails and most importantly, the Bitcoin addresses found in these emails. The Modus-Operandi of the criminals is to
- Create Bitcoin-Address for every Spam campaign.
- In case the recipient’s do pay up the extortion BTCs, the BTC is broken down and transferred to multiple Bitcoin Wallets so as to ensure that researchers find it difficult to track the transactions.
- The breakdown and subsequent transfer of the BTC are done a couple of times, hence at the end of the third iteration, we have close to 100 BTC wallets.
- Finally, all these wallets are consolidated and the BTCs transferred to one single wallet.
During the course of research, we came across numerous wallets with one of them (FJDeT2E1fWb4oZBeub4MH9ennUp5e
Some of the BTC addresses of the campaign:
- 19YayKasVoiRcjcihqmUpjVwvWB9aG
yKCC - 1DtBY4zD7cK35fpbNecpxSaEuEmfu9
uyVG - 1BmXuzjeWdoBKhsX8kJMNBFz5uJzrc
2Gvc - 1HRpxFdKGc7Anb7xfpQf3tmAcH6pph
2ssX - 1FCaw9jXhHveRyLxB54ypCpJ2CtanV
oLC1 - 1MJcj7MdWeKR7eT7PukLG78jcRGf4o
pcsD
Due to the anonymity provided it is impossible to track the identity of the Wallet Owner. Since the month of August 2018, there has been a steady increase in these extortion spam mails.
According to eScan researchers, these emails are a part of a spam campaign and pieces of advice that recipients shouldn’t reply to these emails. However, since this campaign is in its nascent stages, there is a possibility that in near future the emails might be weaponized with the usual variants.
Prevention Measures:
- Ensure to not reply to these emails at all.
- Install and Configure security modules.
- Enable Real-Time Monitoring of Antivirus
- Use Firewall IDS/IPS Intrusion prevention
- Users shouldn’t enable macros in documents.
- Organizations should deploy and maintain a backup solution.
- Most important, Organizations should implement MailScan at the Gateway Level for mail servers, to contain the spread of suspicious attachments.
Related Posts
What is Identity Theft? All that you should know about this form of cybercrime
PayPal’s stablеcoin PYUSD-now accessible through Vеnmo
How to install BetterCap on Windows 11 or 10
Guardians of Data: How Role-Based Access Control Reinvents Security
Google to display only interest-based ads using a privacy sandbox
Ethical Considerations in Digital Banking: Privacy, Data Ethics, and Responsible AI