
Difference between Tor and VPN connections. Which one is the best for your requirements to get optimum security
When it comes to privacy on the internet you should use the internet very … Read more

When it comes to privacy on the internet you should use the internet very … Read more

Here in this article, we will explain 6 different types of firewall used to … Read more

Cyber Security can be regarded as one of the major pillars in today’s world, … Read more

Just like smartphones, we can start using smart home gadgets extensively within the beginning … Read more

Recently on its blog, Google has published few tips to increase the security, privacy … Read more

This section describes the security log or secure log recorded in the Linux OS … Read more

Both good and bad exist in this universe, and the mere world of computers … Read more
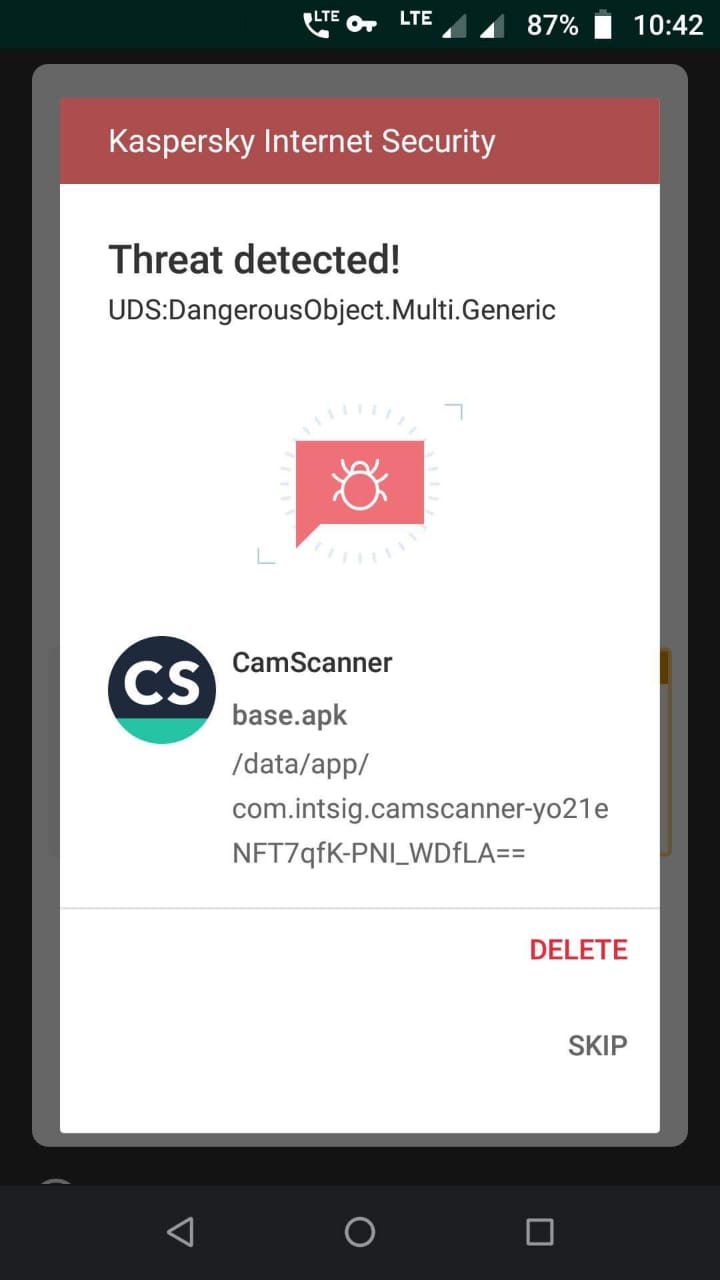
Recently, one of our stalwart readers Surya Partap Singh founder of Aezowie has reported … Read more

With government agencies deploying latest technologies and improving their IT infrastructure at par with … Read more
PremiumAV, launched a lightweight PremiumAV Total Security suit for the end-points to keep data … Read more

Press Release: Trend Micro, a cybersecurity solutions providers now delivers advanced security solutions for … Read more
CoSoSys is a developer of endpoint centric Data Loss Prevention (DLP) solutions and security … Read more

Skybox Security which is a cyber risk management entity has recently announced latest version … Read more

Things you need to know about Pentesting: Penetration Testing or often called PenTesting tools are … Read more