Things you need to know about Pentesting: Penetration Testing or often called PenTesting tools are basic utility applications for any Ethical Hacker job. To be clear we are not promoting any hacking crime or breaking digital security rules, this article is completely for educational purposes.
In this article, we will be discussing Penetration Testing methods and about the needed useful utilities for that purpose.
What is Penetration Testing or PenTesting?
PenTesting is a legally authorized cyberattack simulation against a computer or a server to find out the vulnerabilities and security loopholes of that systems. This process is done by Professional ethical Hackers where they mimic the situation just like an original threat so that the targeted system’s security loopholes can be exploited and all weaknesses can be exposed, also the benchmarking of the targeted pc is to be done so that it can be evaluated how good the system handled itself.
Not only an organization, even the Police Departments, Military and all other government bodies now a day around the world to take this method of PenTesting on account to secure their system and secret data as well as public data from the real hackers and online fraudulent.
Why PenTesting is necessary?
PenTesting just does not exploit the weakness of your systems as it identifies the strength of that system too. Any organization dealing with monetary payment or dealing with confidential user data can asses their risk management capability f they take PenTesting as an essential part of the auditing procedure. Not only annually but also whenever there is an update or system change occurs a PenTesting should be mandatory for both the organization’s and its client’s interest.
The threat even goes deeper when a Research paper by the National Cyber Security Alliance found that almost 50% of the small-scale business and new start-ups fail in the first year due to cyber attacks. In these cases, a term called DIY PenTesting also comes in fourth, which is actually a PenTesting procedure which can be conducted by the users themselves and this is the field where the need for free or cheap, easy to use and dependable PenTesting tools arrives.
Pros of PenTesting:
- Risk and vulnerability detection of a computer-based system.
- Can be used for training purposes for the new interns.
- Enables a clear way for real-time security automation.
- Enables better security and also can gain more trust of the clients.
- Enables a modern way for cyber-forensic investigation method.
Cons of PenTesting:
- Can be disturbing for a business set up as it hampers the processing at the moment when the testing occurs.
- Sometimes false alarms also get triggered which end with time harassment only.
- Time taking procedure in many cases, so time, labour, patience is required.
- At some extent, Pentesting can even damage your devices or system if not administered properly.
- There are many legal issues with Pentesting in some countries about which the tester should be aware of.
The Basic Method of PenTesting:
Reconnaissance (Intel gathering): In this stage, the attacker or the tester will scan the network for all its ports and entry points, and also the system architecture mapping will be done. Gathering information of the user’s data may also be needed for a cold and planned attack especially if social network Pentesting is to be done. To do this kind of job tools like Nmap is very effective and popular.
Scanning: While you have the basic knowledge about the targeted system its time to gather some deeper research data about the system, like vulnerabilities, update schedule, encryption method, weak passwords, system glitches, runtime errors, and XSS errors. A tool called w3af is a good one for this kind of job.
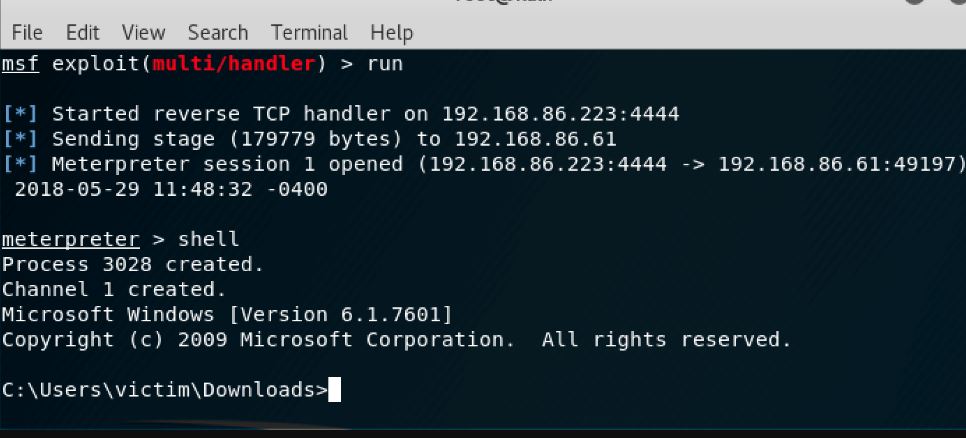
Exploitation: In this stage, the attacker tries to identify the reaction method and reaction time of the system itself after it detects the attack. Here through some specific tools, the weaknesses are exploited, the glitches are used deliberately, and some basic attacks on the security is launched to understand the reaction of the system. Tools like Metasploit is used for this kind of job.
Maintaining Access: This is the most important part as now you have the access or you have found the loophole you have to keep that entry opened up for you until you need it. By mimicking Advanced Persistent Threat (APT), you can put the files or rootkits into the targeted system hidden and dormant from the targeted system’s security protocols. This step ensures the hacker that he has a backdoor entry hidden from the system itself writing for the right time to be used on. For this step, we need the most organized utility application, where Kali Linux serves its service.
Assessment: This part is used by the Ethical hacker or the PenTesters only, where the risk assessment report, benchmarking etc. to be done. According to this report, the IT professionals will be taking a step further to strengthen their security. Also cleaning up the system, reverting back all third-party installation and deleting all rootkits from the system is also to be done. An app like Dradis is a free application for a job like this.
See: 6 Best Linux Penetration Testing Distributions for Ethical hacking
Best Free Tools for Pentesting
Kali Linux Free Penetration Testing
This one is a Linux based open source project available for all for free. The Kali Linux project is very popular among Ethical hackers, PenTesters and hackers. This project is designed and maintained by Offensive Security Project; it is the most popular software distro of its kind. Kali Linux is not for any beginner, prior knowledge of the field is necessary to understand the utilities provided by Kali Linux. Watching tutorial videos on YouTube may help you to understand better. This software comes with many utilities and tools with it,
Wireshark – Network Protocol analyzing tool
Burp Suite – PenTesting tool for a web-based application
OWasp-Zap – Used to find vulnerabilities within a web-based application
Hydra – A very useful tool to launch brute-force password cracking attack
SQLmap – Used to detect vulnerabilities related to SQL injection
Nmap – An effective security scanner to scan a network to understand its architecture.
Features:
- A free product and free service
- Available in 32-bit, 64-bit and ARM architecture
- Lots of preinstalled security and forensic tools make it a one-stop shop for many solutions
- Multi-lingual support
- Very active and large community
- One of the most maintained, well-funded, well developed free, open source PenTesting project on the market
- Can be installed using live-boot installation via USB drive
- A well-organized archive for various PenTesting tools for various kind of needs including packages for wireless,
- Web-based applications, Forensic needs, software defined radio etc.
Metasploit
This one is one of the most advanced and very popular frameworks which is used for Pentesting by the experts. The Metasploit tools are also renowned as one of the best development tools for exploiting codes and this tool can be used to execute those codes as well. Though reportedly many hackers do use this tool for illegal system penetration purposes as using this tool, rootkit and exploiting progs can be re-engineered.
There is an alternative to this application called Nessus, which is a paid commercial product.
Features:
- Available for free.
- A very good and hard-working community is working behind this application. The community is working on providing the users more ready-made exploiting modules, though if you have the skill you also can build your own set of progs and modules.
- Metasploit offers more than 3000 ready-made exploits and multiple payload options with those. Even the infamous exploit used by WannaCry ransomware is also available in Metasploit.
- Metasploit is also developed by the Offensive Security Project, so they have built-in plugins for Kali Linux as well.
- An auto recording system is included with this framework, which can record the data in its own internal database.
- It also has Nmap integration from Kali Linux.
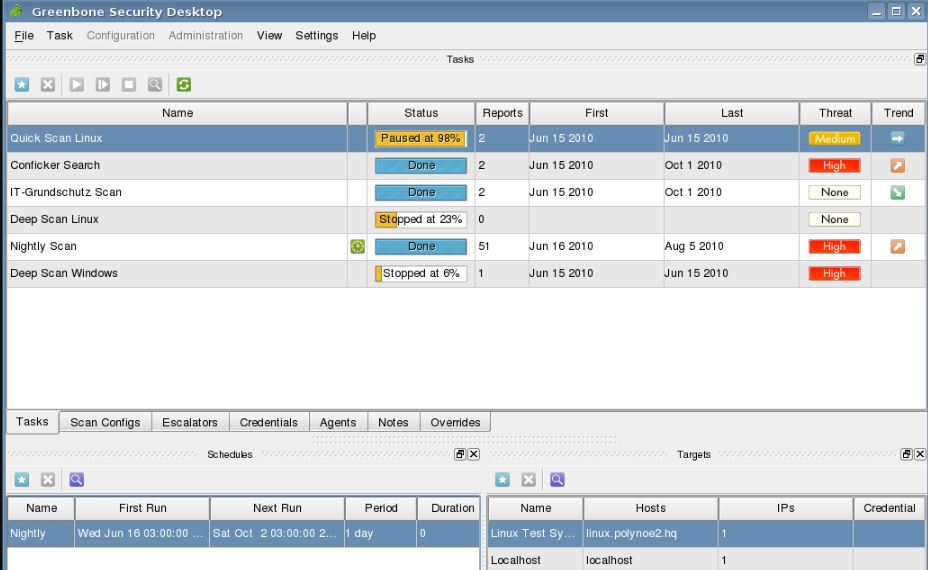
OpenVAS – Penetration Testing tool
OpenVAS is the free distro of a software package which is used for Security Scanning and also consists of many tools and services to map and Exploit a system. The Scanner program needs a client utility to be installed in order to work in a Windows pc. This application gets daily updates of Network Vulnerability Test, the news feed updates are also very regular. In Simple OpenVAS is a Network Vulnerability Scanning application.
There is some alternative application also available for this package namely, SolarWinds Network Configuration Manager (Free trial mode), Paessler Network Vulnerability Monitoring with PRTG (Free trial mode), ManageEngine Vulnerability Manager Plus (Free trial mode) etc.
Features:
- A free piece of tool
- Contains a huge database of vulnerability identifier
- It has a Concurrent scanning capability with other tasks
- It can be set to run scheduled scans on a targeted system
- It has a result manager which manages the False Positive result automatically.
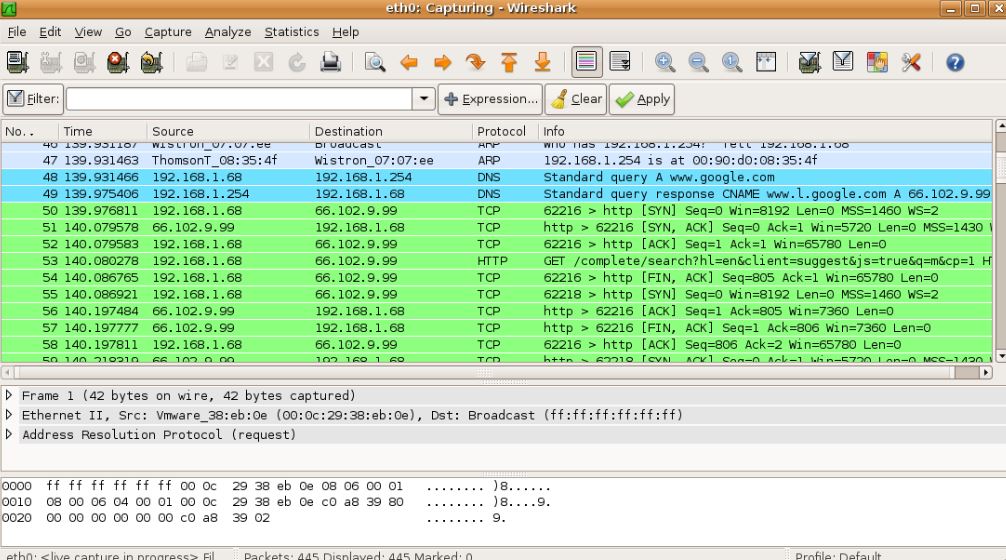
Wireshark
It is a Network monitoring application, and it is claimed that this one is the best in its class. The claim is not wrong at all, as this one is the best you can expect from a network monitoring application. For the utilities this application has many people do think that using this application is illegal which is actually wrong as it is illegal only when you monitor a network for which you do not have the authorization. To monitor the network traffic this application does monitor every single data packets of every single request between the client station and server station. But this application can be used for measuring and monitoring data only, using this application you cannot manipulate data. Though reportedly this application used to contain glitches which ended up as security vulnerabilities by itself so using the latest version is recommended.
This application has a huge use in the sector of a federal investigation, forensic investigation and spying on the hostile network and suspects digital footprints.
This application is a little tricky to use, if you are looking for a simple solution then try Tcpdump.
This kind of application is also known as Packet Sniffers or Network Analyzers.
Features:
- This application supports a huge number of protocols including IP, DHCP, AppleTalk, BitTorrent everything. So, even your torrent downloads cannot go unnoticed from any of the end if someone is really interested in your data.
- It has the highest no of downloads, which reflects the popularity and trustworthiness of the application. Many organizations use this application for their own Network troubleshooting as well.
- It also contains many documentations for new users along with many training tutorials. Along with a Network Activity scanner the application also consists of an Application Programming Interface (API), for capturing Network traffic as well.
- There is a plugin called Promiscuous Mode, which enables capturing the data packets across the network even if they are not associated with the correct address, which means even using VPN you cannot escape the sight of Wireshark.
W3af- web Application Attack and Auditing Framework utilities.
This application is very easy to use application. The main focus of the application is on Web Application Attack and Auditing Framework utilities. This application is more likely a dubbed edition of Metasploit with a more Emphasis on Web-based applications. Though this application contains many bugs which reduce the performance as well make lower the bar of trustworthiness. Though the latest version is claimed to be free from all bugs related problems.
There is a very good alternative program for this one named Zed Attack Proxy (ZAP). Instead of Python like W3af; ZAP uses java enact.
Features:
- Plugins made of Python code is used to identify the vulnerabilities of the targeted system. The plugins sent HTTP requests to forms and use quarry string parameters to identify the errors, glitches, run-time error and misconfigurations.
- Easy to learn, easy to use GUI.
- It also features the Black-box scanning techniques in order to find the vulnerabilities in a targeted web-based application.
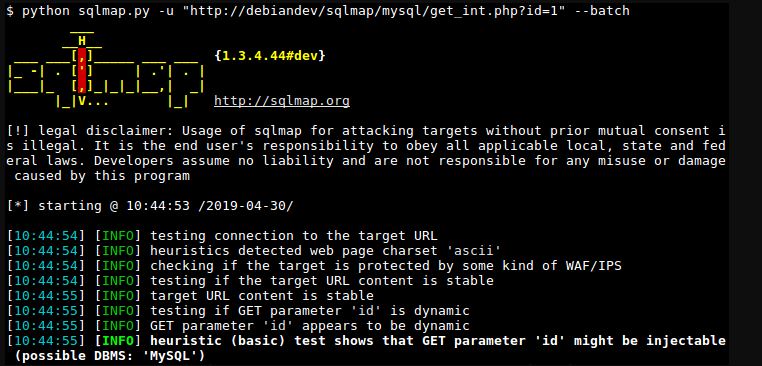
SQLmap
Using a tool like SQLmap requires much more skills than the other ones. SQLmap deals with the process of detecting and exploiting SQL injection flaws, which help the hackers to get access to the back-end database servers.
If you are looking for an alternative to SQLmap, SQLNinja is the one you should look for. But SQLNinja is also not for a beginner, so learning about the SQL injection and all may need some time.
Features:
- A free application also an alternative one.
- It supports MySQL, Oracle, PostgreSQL, Microsoft SQL Server, Microsoft Access, IBM DB2, SQLite, Sybase, Firebird, SAP, MaxDB, HSQLDB and Informix DBS. So, all popular database management system using SQL can be attacked via using SQLmap or SQLNinja.
- It supports all the SQL injection techniques, i.e. Boolean-based blind, Time-based blind, Error-based blind, UNION query-based blind, Stacked queries and Out-of-band. In simple words, it is a very complete package for a specific job and this application is the best at it.
The Social-Engineer Toolkit (SET)
This application is engineered for attacking against the human elements on a system. It includes various kind of custom attack vectors which let the user make an attack on the targeted system in no time. This application’s main target is to automate and improve the response on the social-engineering attacks which are happening every day. It has tools using which you can create a malicious website, you can send emails containing malicious files or autorun trojan files. You also can create and send SMS and even generate QR Code to any specific URL.
This application is not a cup of tea for any pro hackers but it is an essential tool for the PenTesters and ethical hackers.
Features:
- This one is a command-based tool, the commands are very easy to master, and this one is very easy to use the tool.
- You can find many tutorials on GitHub if you want to learn thoroughly.
- This application uses Python coding, it is aligned with the PenTesters Framework (PET), the scripts support Debian, Ubuntu, ArchLinux etc.
Nmap
This application is in existence since the 90s. It was made not for PenTesting but now it is one of the most commonly used application by the Ethical Hackers and the pro Hackers to identify their targets and exploit their targets. Nmap provides the user with a map of a target network in a very comprehensive way. The result shown by the Nmap scanning includes the data of target’s OS running, which Internet browser is in use, what kind of firewall the pc has etc. Using the scripts, the result can become more extensive. You can find many Nmap scripts on the internet.
Features:
- Supports many techniques for mapping out the target network, the result includes data like OS, Browser, third-party services, IP filters, firewalls, routers, online security antivirus application etc.
- Most of the OS are supported by Nmap, including Linux, MS Windows, FreeBSD, OpenBSD, Solaris, IRIX, Mac, OSX, HP-UX, NetBSD, Sun OS, Amiga etc.
- Both the command-line interface and Graphical user interface are available.
- Free application and a very renowned and dependable one even for a professional job.
Dradi-Penetration Testing
In a PenTesting to share the info and collaborate the data an application like Dradi is a must to have. Dradi is an open source framework which keeps and maintains the central repository of all the data related to a PenTesting project, from where you can keep a track on the job and as well as on the targeted system.
Clearly, this one is not a hacking tool at all, this one is an associated tool for an Ethical Hackers job to keep it organized.
Features:
- It is a free and open source application.
- The application is platform independent.
- It has a good community forum.
- The application automatically combines the reports from the connected tools and generate a single summary of the reports.
- This application can connect with many different tools including burp, Nessus, Nmap, Qualys, etc.
Wrapping UpPenTesting tools
Doing PenTesting or practising Ethical Hacking or White Hat Hacking is not illegal at all, but while doing live hacking the target system’s authorities’ consent must be taken. Even at the professional level, the employer’s consent must be taken for own safety from any future lawsuit.
For the beginners, there are many open to all network and servers available in which you can practice your hacking skill and techniques without any consent or lawsuit. You can search for the top vulnerable sites on the internet to find out about the websites and web services which let the new learners practice their hacking skills without any price or legal problem.



Related Posts
What is a juice-jacking attack? How can we be safe from such attacks?
How to install Winget package manager in Windows 2022 Server
How to View Listening Ports Using Netstat
How to Install Pygame Zero on Windows 11
Single Command to install Android studio on Windows 11 or 10
What is Identity Theft? All that you should know about this form of cybercrime