Traceroute is a nifty tool that is used in Linux or Unix based operating systems such as Windows, MacOS, and Linux (Ubuntu). To use this tool there are some specified commands those help the administrators to trace the routing of the data packets from the origin point to the destination. In short, it prints the route packets trace to the network host. Nowadays so many computers, server or devices are avoiding to get trace or ping because of the DDOS attacks. However, the traceroute command is still useful to find out the bottleneck inside or outside of your network where you are working. We already have created a tutorial in which we have given a way to run the traceroute command on Windows systems: Here is it- How to use Traceroute in Windows 10/8/7.
If you are not a Windows user and Linux is what you up to then this tutorial is for you; which let you know how to run Traceroute command on Ubuntu Linux and more or less the command is same for other Linux versions too.
- First of all, go to your Ubuntu or other Linux version. Here we are using Ubuntu.
- Open the command terminal by searching through apps or just press the CTRL+ALT+T shortcut keys from the keyboard to fire up the Terminal.
- By default, the Traceroute tool is not installed on the system, unlike Windows. So, we install the Traceroute using the command: sudo apt-get install traceroute
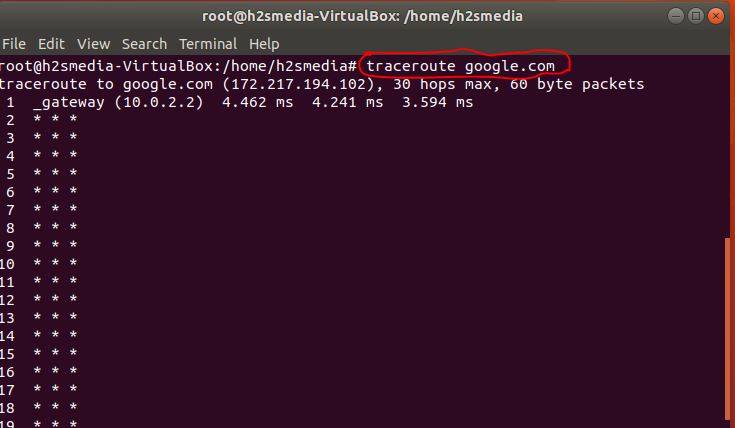
- Once the Traceroute tool is installed, use it with the hostname or IP address that route you on to find out.
- The command will be like this: traceroute example.com or traceroute 192.168.5.5
Further parameters to use the Traceroute command in the Linux operating system like Ubuntu.
traceroute [ -46dFITnreAUDV ] [ -f first_ttl ] [ -g gate,… ] [ -i device ] [ -m max_ttl ] [ -N squeries ] [ -p port ] [ -t tos ] [ -l flow_label ] [ -w MAX,HERE,NEAR ] [ -q nqueries ] [ -s src_addr ] [ -z sendwait ] [ –fwmark=num ] host [ packetlen ]
The way to use these options or parameters with traceroute is traceroute along with the option. For example traceroute -4
Options:
-4
Use IPv4
-6
Use IPv6
-d –debug
Enable socket level debugging
-F –dont-fragment
Do not fragment packets
-f first_ttl –first=first_ttl
Start from the first_ttl hop (instead from 1)
-g gate,… –gateway=gate,…
Tells traceroute to add an IP source routing option to the outgoing packet that tells the network to route the packet
through the specified gateway (most routers have disabled source routing for security reasons). In general, several
gateway’s is allowed (comma separated). For IPv6, the form of num,addr,addr… is allowed, where num is a route header type (default is type 2). Note the type 0 route header is now deprecated (rfc5095) (maximum 8 for IPv4 and 127 for IPv6)
-I –icmp
Use ICMP ECHO for tracerouting
-T –tcp
Use TCP SYN for tracerouting (default port is 80)
-i device –interface=device
Specify a network interface to operate with
-m max_ttl –max-hops=max_ttl
Set the max number of hops (max TTL to be reached). Default is 30
-N squeries –sim-queries=squeries
Set the number of probes to be tried simultaneously (default is 16)
-n
Do not resolve IP addresses to their domain names
-p port –port=port
Set the destination port to use. It is either initial udp port value for “default” method (incremented by each probe, default is 33434), or initial seq for “icmp” (incremented as well, default from 1), or some constant destination port for other methods (with default of 80 for “tcp”, 53 for “udp”, etc.)
-t tos –tos=tos
Set the TOS (IPv4 type of service) or TC (IPv6 traffic class) value for outgoing packets
-l flow_label –flowlabel=flow_label
Use specified flow_label for IPv6 packets
-w MAX,HERE,NEAR –wait=MAX,HERE,NEAR
Wait for a probe no more than HERE (default 3) times longer than a response from the same hop, or no more than NEAR (default 10) times than some next hop, or MAX (default 5.0) seconds (float point values allowed too)
-q nqueries –queries=nqueries
Set the number of probes per each hop. Default is 3
-r
Bypass the normal routing and send directly to a host on an attached network
-s src_addr –source=src_addr
Use source src_addr for outgoing packets
-z sendwait –sendwait=sendwait
The minimal time interval between probes (default 0). If the value is more than 10, then it specifies a number in milliseconds, else it is a number of seconds (float point values allowed too)
-e –extensions
Show ICMP extensions (if present), including MPLS
-A –as-path-lookups
Perform AS path lookups in routing registries and print results directly after the corresponding addresses
-M name –module=name
Use the specified module (either built-in or external) for traceroute operations. Most methods have their shortcuts (`-I’ means `-M icmp’ etc.)
-O OPTS,… –options=OPTS,…
Use module-specific option OPTS for the traceroute module. Several OPTS allowed, separated by a comma. If OPTS is “help”, print info about available options
–sport=num
Use source port num for outgoing packets. Implies
`-N 1′ –fwmark=num
Set firewall mark for outgoing packets
-U –udp
Use UDP to a particular port for tracerouting (instead of increasing the port per each probe), default port is 53
-UL
Use UDPLITE for tracerouting (default dest port is 53)
-D –dccp
Use DCCP Request for tracerouting (default port is 33434)
-P prot –protocol=prot
Use a raw packet of protocol prot for tracerouting
–mtu
Discover MTU along the path being traced. Implies
`-F -N 1′ –back
Guess the number of hops in the backward path and print if it differs
-V –version
Print version info and exit
–help
To get help on commands
Arguments:
+ host The host to traceroute to packetlen The full packet length (default is the length of an IP header plus 40). Can be ignored or increased to a minimal allowed value
Related Posts
What is ipconfig on Windows CMD used for?
Top 10+ Email Clients for Windows 11 or 10 – Free and Paid Apps
7 Free and Best Open source VPN Server Software
Vboxmanage command not found in Windows CMD or PowerShell
8 Best ways to start Command Prompt in Windows 10
How to show hidden files in Windows 10 using Command prompt