VPN or Virtual Private Network can seem like a complicated topic but the usefulness of this technology is really worth reading about it. Though it is a little-complicated system, if you go through this article thoroughly we believe any doubt of yours about VPN will be diminished. In this article we will be discussing most of the frequently asked question about VPN, we will start from a beginner level. Along with the explanations, we will also recommend you some VPN tools which are free and easy to use, of course, we are not promoting any of those products, so you can also try any other available VPN tool over the internet.
Q1. What is VPN in simple words?
A VPN (Virtual Private Network) is a technical service which let the user access the web safely and privately by routing the connection through a different server and hence hiding the online activities. Which makes it harder or in some case impossible to track back the user IP.
Q2. How does the VPN system work?
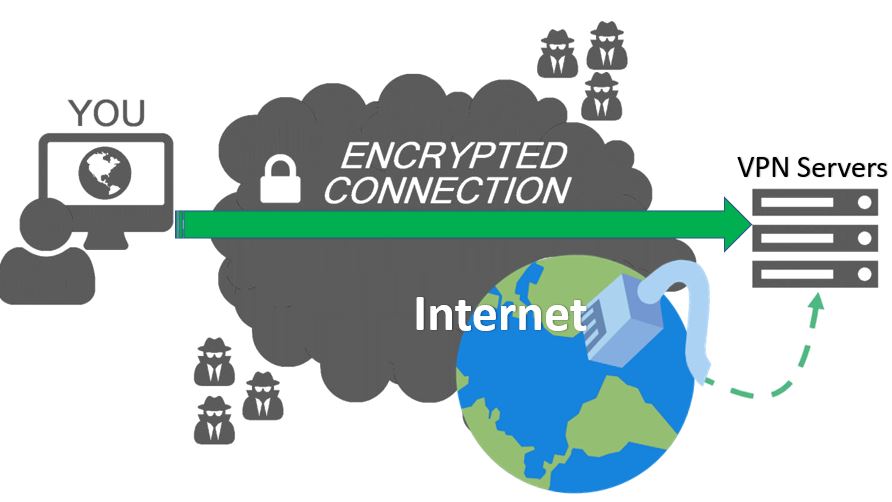
First, you start the VPN client software from the installed service of yours. This software is programmed to encrypts your data way before your personal internet service provider or any public internet service provider tracks it. Then the data goes to the Private Network of your VPN software’s server and from there the requesting IP address got changed according to that server’s algorithms and then the request goes to the destination website and server. The destination website can be anything like your bank website, video sharing website, music website or search engine. Then the destination server checks your data as it is coming from the VPN server and its location, it is not easy for that destination server to track your actual IP address.
When anyone connects to the internet without a VPN then any interested and authorized party and even some hackers can track and see what you are doing over the internet. What confidential information you are using, even what kind of restricted websites you are trying to access. This way not only they can keep their eyeballs on your all online activity but also, they can control it by using your IP address and server IP. An authorized party even can stop you from accessing any specific website or data over the internet. In short which confirms you have almost no privacy in your online activities.
If you are surfing around fun websites like listening to music, watching videos at YouTube it does not matter if someone is tracking you. But in the case of online banking, confidential email, sharing personal details then no privacy become a very big challenge.
When a user uses VPN service the data got encrypted by the VPN application goes to the ISP and from there it goes to the VPN server and from there it goes to the requested destination server. The requested destination server also sent the replies to the VPN server then it reports back to the ISP server then the data come back to your terminal and got decrypted by the VPN application.
- The destination site sees the VPN server as the traffic origin, it does not see you or the user exact IP address.
- No one can easily identify the user’s computer’s IP address, so it is very hard for them to track the original source, or to track what data is actually transferred and by whom.
- The data also got a protective shield of encryption which makes sure no raw data fall into some unwanted or prey people’s hands.
Q3. How secure a VPN service itself?
There are many debates about the VPN and its security features among the IT experts and experienced users. Actually, all the VPN service application available in the market are different in terms of their security protocol. There are a couple of points those derive the main factors:
- The limitation of the VPN service used by the application providers.
- Legal and policy limitations which are affecting what can be done with any specific VPN application.
- It also depends on the factor from which country the user is using the VPN and what are that country’s internet activity monitoring policies and in between that how the VPN provider is implementing their technology.
- The main security feature of any specific VPN application depends on their VPN protocols. The most common protocols used by most of the VPN providers are discussed in brief below.
- PPTP (Point-To-Point Tunneling Protocol) – This is one of the oldest protocols in use, designed by Microsoft itself. It works on almost all kind of computers regardless of how old they are and what OS they are using. By today’s standard, it is not that much secure, most of the country’s online activity monitoring authorities have cracked this security feature. If you VPN provider is offering only this type of security then you should avoid it.
- L2TP/IPsec (Layer 2 Tunneling Protocol) – This is a combination of PPTP and L2F (Layer 2 forwarding) protocol (designed by Cisco). Though this technique establishes a connection on each end of the data tunnel, the execution procedure is not that secure according to experts. The addition of the IPsec protocol improves the security very much. Though there are debates about that most of the Intelligence and security agencies of the world can break this security protocol. Keeping which on mind you can also avoid the use of this kind of protocol if you are too concerned.
- SSTP (Secure Socket Tunneling Protocol) – This protocol is also built by Microsoft. The connection got established with some SSL (Security Socket Layer)/TLS encryption (standard web encryption in present days). This has a very good quality symmetric-key cryptography which enables well strength in protection, in this procedure only the specific parties which are involved in the data transfer can decode the transferring data. This is a very secure solution in terms of VPN.
- IKEv2 (Internet key exchange, Version 2) – Again, this protocol is also built by Microsoft. It is actually an upgraded version of the previous Microsoft based security systems. For sure this one of the secure VPN security solution.
- Open VPN – This procedure takes the best parts of the above said security protocols and overcome most of the flaws of those. It is mainly based on the SSL/TLS technology and it is an open source project. Which means it is constantly being updated and improved by the IT pros and enthusiasts. This enables the security by featuring data decoding by the two participating parties only in a data transmission. It is the most versatile and secure VPN protocol out there in the market.
In general, most of the popular VPN application let the user choose among multiple types of security protocols. The more secure connection the user chooses, the more secure the connection become. But, in some case more secure connections tend to be a little slow because of their lengthy and complex processing.
But to remember, not all devices will allow the user to use all these above discussed protocols. Since most of them were built by Microsoft, all of them can be used on Windows PCs for sure. For Apple devices, there are some limitations, L2TP/IPsec is the default protocol for iPhones. While talking about Android devices they have some problems of its own, which will discuss later in this article.
Q4. Is it Legal to us VPN application for personal usage?
All good VPN service provider companies will do their best to ensure the protection of your data, your privacy, your overall security on the web. But remember that they’re still subject to the law in the jurisdiction they’re in, which can affect their service anytime. To ensure the protection at its best they often use multiple servers and they also often change their server IP and server locations, so that they do not allegedly cross any legal red lines.
Depending upon the local law of that specific country where the VPN service provider was established, the company may be forced by court of that country to share whatever records they have regarding any of their user’s activity, there even can be international agreements between countries and those type of companies to share information in these cases. If you go through the details of most of the renowned VPN service provider companies, you may find that they are established in a country which doesn’t have any such agreements or law for this kind of cases.
So, it is true that you are only secure with a VPN connection if it’s not only willing and technically capable of keeping your data safe and private, but also if it has the legal immunity to do it.
While answering the question of using VPN for personal use is legal or not, the answer is YES. But not always (with exception). VPN as a concept is relatively new in the legal world, so not all jurisdictions have managed to keep up with that change. This means that the rules are murky and can be interpreted in many ways depending upon the situation and the importance of any specific case. VPNs seem to be okay to use in most of the countries. Countries like USA, Canada, UK, Netherlands, India, most of the African countries, Australia, New Zeeland have no such rules about VPN, so you are cool within these countries. Using VPN is not okay in countries like China, Turkey, Iraq, UAE, Belarus, Oman, Russia, Iran, North Korea, Turkmenistan etc.
Q5. Does a VPN Make the user Fully Anonymous Online?
In simple word, NO. But the extent to which it does make the user anonymous is still very impressive. In most of the cases you will find that the need of yours already been satisfied by staying anonymous, hence you may never need to explore the highest extent of the service.
Without a VPN service, your connection is completely open, hence your Internet service provider, the cafe Wi-Fi router administrator or any media server along the way or a person with the just the right tools and knowledge can look at your data and steal it. Using a VPN solves many of those problems, especially in terms of personal online security by encrypting your transmission and making it appear as if it’s the server itself that’s making the connection and not you. Which makes it harder to track & hack. The hacker party also will not be sure about the that which of the data is exactly yours which makes you immune to this hacker threats.
While getting a VPN service go through their user manual and website and research about their product to know most you can. Look for the answer to the below-listed question which will help you realize that how secure you are while you are using their VPN service product.
- Does the VPN service keep logs (in user’s PC or in any server)?
- The jurisdiction under which the VPN is established. In some cases, they might be legally forced to keep records.
- Does the service keep payment records? Do those records include identifying information (id, password, reg no)?
- What encryption protocol they are using? Is there sufficient encryption and a secure connection protocol available?
Not all the VPN application will protect you the same. So, choose wisely for best security and least hassle.
Q6. What kind of logs, does a VPN keep about the user?
- The logs a VPN application and the VPN server itself keeps about the user and the data transmission significantly affects the level of anonymity of the user as well as the privacy of the user. The logs a kept by the provider may keep data like,
- User activity
- IP addresses
- Connection/disconnection time-stamps
- Devices used
- OS used (not in every case)
- Payment logs
Any such kind of logs makes you a less anonymous than you think you are since your IP can be connected to a given browsing session that you had. Of course, if you or a general person is trying it is nearly impossible to track these data, but an agency or authority with such power or knowledge can do so for sure. Note that, many services state that you have privacy on their sales material (in the advertisement), but you need to look at their privacy policy to see their actual procedure of keeping logs and what data they actually keep.
Q7. Can VPN be used for Torrenting?
- In general, YES, but that also depends on the specific service you’re looking for and also what kind of material that you are torrenting. The purpose also depends, whether it is for personal or commercial usage.
- Torrenting is a common name for a specific type of protocol or technology used to transfer data and files over the web, but not the actual types of files or not the direct files. Although it gets a lot of bad press overall around the world. Remember, it is perfectly okay and legal if you’re transferring files that you have the rights to. Piracy, on the other hand, is completely illegal regardless of the tools that you use to do it. But in most of the cases, the torrenting is being used for the sake of digital piracy, which actually makes a misuse and malpractice of this technology.
- When it comes to the point of security while torrenting, it all comes down to the VPN’s policies regarding things like logging or sharing your user data which we discussed earlier. In general, if a VPN doesn’t keep logs overall, they also don’t keep them for your torrent activity, which makes it safer for all of your purposes.
- Another aspect worth considering when choosing a VPN service for torrenting is the upload and download speeds that the service can offer. As the VPN service employ multiple media servers and encryption method it tends to be a little slower. Of course, this sort of information can be hard to find and most of the time you only find out about it after using the product.
Q8. Issues of VPN while using it in Android or iOS?
- Yes, you can use VPN in Android and iOS. Many of the top VPN services out there in the market also let you download their own- or third-party mobile apps for either Android or iOS. Both platforms let you set up a VPN connection very easily compare to a Pc. For instance, on iPhone, you can do that in Settings > General > VPN.
- With all that being said, be careful while you’re tempted by any of the free VPN apps for either Android or iOS. As in a study, it has been revealed that 38% of those apps include malware, 84% leak users’ data and 75% use tracking libraries. So, in that VPN, privacy is a myth.
Q9. Free VPN vs Paid VPN –
- Running a good VPN service costs serious money, like all other IT companies they also need robust server systems, big data transfer engines, infrastructure, employees, office spaces and so on. So, if the company is offering the service for free, consider what compromises you may have to make. Consider the points like; Are they logging activity for their own reasons or jobs? Are they displaying their own ads in between use of their product? Is your data being sold to a third party by the VPN service providers? etc.
- Paying for a VPN isn’t a huge investment actually. Some of the best VPN do charge you about $3-6 a month, exchange for that price you can have peace of mind and improved online privacy. If you opt for the annual package then the monthly price also do reduce very much, so choose while you want to try VPN for free or you want to ensure the best quality service, remember it is a matter of your and your family’s personal digital security.
Q10. How Do I Install a VPN on My Router?
- Installing the VPN service into the router is the best and easiest way to make sure that all the devices connected through that router put through a safe connection. In that case, you no longer need to install VPN in each of your devices individually.
- To do it you first have to make sure that you are using a VPN supported router. You can check it in the user manual or in the router’s company website. The specific steps involved in setting things up differ from service to service and router to router. Your specific VPN provider likely has a dedicated section on their website to help the customers in this installation procedure and also in the product manual all the steps are well explained. You can also watch some tutorial videos on YouTube to understand better. Installation procedures are made in a way which is very simple and involves you logging in to your router normally and then filling out a couple of standard forms which is easy to handle for anyone. Then also if you need you can definitely contact someone who is expert in this.
Q11. When To use VPN? When Not to use VPN?
If you are looking for the below-listed points then you should definitely go for VPN as it is the solution of your need:
- It encrypts your activity on the web.
- It hides your activity from anyone who might be interested in your data or digital footprints.
- It hides your location, enabling you to access any geo-blocked content or website like, Netflix, Hulu or even any Pornographic website or blocked torrent sharing website.
- Makes you more anonymous on the web.
- Helps you keep the connection protected when using a public Wi-Fi hotspot (like in cafeteria, college, airport etc.)
While talking about when not to use it:
As predictable as this may sound, there is no good reason not to use a VPN only if you’re taking your online security and privacy too seriously. Though VPN adds an extra layer of security while browsing the internet over the SSL. There are actually not many downsides of VPN, but VPN can slow your surfing speed down and downloading-uploading activities also can become slower sometimes, if you consider these as negative points then you should rethink about it.
Before getting a VPN service do not forget to check the public and customer reviews on that VPN over the internet.
Other useful resources:
- How to add Cloudflare to VPS/ Dedicated / Shared hosting servers?
- How to choose the best VPN service? Things to see to get the best VPN service in budget
- How to use Turbo VPN to open & access blocked websites on Android Phones
- Top 5 Free and Paid VPNs to go anonymous over the internet: Pros and Cons
- 6 Free and Best Open source VPN Server Software
- 4 Best Open source custom router firmware
- Top best Torrenting sites 2018 to download your favorite contents
- 5 Best Privacy Browsers For Private Browsing Anonymously
Related Posts
7 Free and Best Open source VPN Server Software
Top 8 Internet Browsers With Built-in VPN For Android & iOS
VPN – Virtual Private Network: Usage and types
The 5 things that a VPN service cannot do for you
Top 7 different ways of increasing the speed of a VPN connection
Proxy vs. VPN- Which one you should choose for your privacy on web?