Kali is the most popular and commonly used Linux by hackers to perform penetration testing or hacking. However, nowadays “hackers” term is not only used for the wrong group of people to perform “Black hat hacking”. There are ethical hackers those do white hat hacking to find out the security loopholes and make our system more secure and better.
Hence, Kali Linux distribution is widely used specialized Linux for security and penetration testing of IT systems. Out of the box, Kali Linux which is based on Debian offers numerous tools to perform various hacking and testing tasks.
For the Desktop interface by default, KALI uses XFCE, however, GNOME & KDE are also available. It is an open-source project, developed by Offensive Security, and is aimed primarily at professional users but can also be used by private individuals.
Earlier Kali Linux was known as BackTrack. It can be booted into a virtual machine and installed on a 32-bit or 64-bit x86 system as well as on computers with ARM architecture.
Even the single-board computer Raspberry Pi can also be operated with the Kali distribution. For some Android-based devices, the penetration testing platform NetHunter exists, which originated from Kali Linux.
Well so far we have learned about Kali Linux but what is the reason, why hackers want to use Kali Linux? Here in this piece of content, we will learn about the popular reason that made hackers and Testers use the Kali Linux distro.
Check out the Advantages of using Kali Linux.
1. Kali Linux is free and open source
Kali Linux distro is available to download and use free of cost. Of course, when a user doesn’t have to pay anything to use an operating system, it becomes popular. Being an open-source project, everything is transparent no hidden codes that worry developers or hackers. Even they can track the development of Kali Linux.
Also, beginners or learners don’t need to pay some hefty amount to start learning ethical hacking. They can install it on virtual machines or even can use Kali Linux as their primary OS.
2. Available for both 32-bit and 64-bit systems
Kali Linux still not only supports modern systems but also older ones running on 32-bit processors. This makes users utilize the power of their old computer system or even mobile devices.
The system requirement of Kali Linux is also not resource-hungry. If you are planning to run Kali Linux on low-end PC systems, without a desktop interface then it required 125 MB of RAM whereas 512 MB for better performance. To OS store data it required 2GB of free hard disk space.
Those who want KALI Linux with a graphical interface XFCE need 2GB of RAM and 20 GB of free hard disk space least.
Besides its availability as ISO image, Cloud, and Virtual Image; Windows users can download the WSL Kali Linux. Of course, the installation or operation of the live DVD on a VM is also possible here. If you want to run the distribution as a VM from the outset, you can also download Kali as a virtual appliance. Whereas, as a cloud solution it is available in Amazon Web Services and Microsoft Azure.
3. Kali Linux’s hundreds of Testing & hacking tools
One of the biggest reasons why hackers use Kali Linux is because of the hundreds of tools it offers; that are meant to carry out various types of security and penetration testing. Such as tools for information gathering, reverse engineering, sniffing & spoofing; WLAN attacks, password cracking, exploitation, and forensics, and many more…
The tools of Kali Linux are available to users via quick access from the desktop. Since the programs are periodically re-sourced from the Debian repository, it is ensured that the latest versions are available.
Out of hundreds of Kali Linux tools, some of the popular network tools are Wireshark which is a graphical network sniffer tool, and Ettercap, a network manipulation tool. For Wireless networks, Kismet is available which is a passive sniffer. To explore and analyze networks, the Nmap scanner tool can be used. In similar ways for network packets forgery Nemesis tool is available.
Other popular tools Kali includes are Maltego software used for intelligence, forensics, and collecting data; the Social-Engineer Toolkit (SET), John the Ripper, a program for testing and cracking passwords, or the exploit framework Metasploit. It allows various attack methods to be carried out in order to test the vulnerability of systems via exploits.
Kali Linux doesn’t just have small open-source tools that can be used to check or ensure network security. Well-known tools such as OpenVAS, which can perform comprehensive security analyses, can also be integrated into Kali.
4. Due to the Forensic Capabilities of Kali Linux
With the availability of various forensic tools, Kali Linux is not just limited to testing networks or hacking some computer systems. Hackers, testers or developers, or even a newbie with computer knowledge can use Kali to analyze disks or recover deleted data. Just, for instance, look at its Autopsy tool that can help a user to check out long-deleted data on a drive as long as it has not yet been overwritten. Even using this tool, hackers can retrieve memory dump, information about running applications, and processed data.
Guymager, Foremost, Hashdeep, DDrescue, Scrounge-NTFS, and Pdf-parser are some popular tools for data recovery.
5. Privacy or no data tracking
Unlike Windows and other OS where the third party tracks the user data such a problem is not with Linux distros such as Kali Linux.
Kali distro is one of the best secure distorts for testing and ethical hacking. We can either install it on our computer system or can boot it in a LIVE environment using a USB drive to leave no trace on the system. Furthermore, combined with browsers such as Tails and Tor network hackers become anonymous over the internet.
FAQs
Is Kali Linux harmful to PC?
No Kali is just like any other Linux operating system. A user can install it to use as the primary OS to perform day-to-day tasks. However, as this Linux is crafted to use by testers and hackers and because of so many tools to support them, this Linux is not recommended for general regular PC users. Nevertheless, beginners and learners are always welcome to use this Linux without any problem.
What is Kali Linux used for?
The key use of Kali Linux is to provide a set of open-source tools for information gathering, reverse engineering, penetration testing, sniffing & spoofing; WLAN attacks, password cracking, exploitation, and forensics. With the benefits of privacy and open source.
Do pro hackers use Kali Linux?
Yes, security professionals and enthusiast hackers do use Kali Linux and similar distros such as Parrot Linux, BlackArch, and Archstrike. However, experienced hackers even can use any minimal Linux to install the tools they required for carrying out the testing and hacking tasks.
Can you get in trouble for using Kali Linux?
As long as you are using Kali Linux for legal security and penetration testing you will not get into some trouble. However, the movement you start using it for Black hat hacking, in short for some abusively and illegal purpose and if found by the authority, they can take action against you. For example – Password cracking, sniffing data, overloading server systems with some harmful intention, or hacking networks for spying and ransom.
For any attack or test on some other property, the service providers who use the Linux distribution for such services require permission to carry out tests from authorized persons or management. Furthermore, as the Kali Linux distribution includes tools that can be used for hacking, hence unlawful use is punishable.
What is the disadvantage of Kali Linux?
So, far we have talked only about the advantages of Kali Linux, there are some disadvantages to using it as well.
- Kali would not be a good option for new users.
- Difficult to use by regular general Desktop users, especially who are just switching from Windows.
- Slow as compared to other lightweight Linux distros. Hence, old system users may face problems when they used it with a GUI desktop.
- Kali is not offering anything that an experienced Linux user cannot install on any other Linux system.
- Only good for penetration and hackers, not for developers.
- It is meant for only Skillful and experienced users.
Should I install Ubuntu or Kali?
Ubuntu Linux is developed to target Servers and regular desktop users whereas Kali Linux is for Cyber Security and Penetration testing users. Hence, decide in which category you fall and install Ubuntu or Kali Linux accordingly.
Is Kali Linux faster than Windows?
Yes, the Kali Linux system requirement is less than Windows, hence Kali Linux can run faster compared to Windows and even on old hardware systems.
Is Kali suitable for beginners?
No, Kali Linux shouldn’t be used by beginners who don’t have any knowledge of Linux and its commands. He or she must start with another Linux system such as Linux Mint or Ubuntu.
Does Kali Linux have viruses?
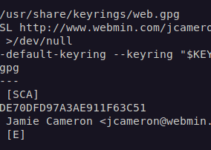
Viruses and Malware don’t affect Linux systems as Windows because of the permission system and its working. Moreover, out of the box, Kali Linux ISO from its official website will be without any virus or malicious modification. For more confirmation, the users can match the hash code of the ISO image they get for the installation.
How much RAM do I need for Kali Linux?
For the command line interface, Kali Linux users need a minimum of 128MB of RAM, and recommended one is 512MB. Whereas Kali with XFCE desktop requires at least 2GB of RAM.
Is Kali Linux completely free?
It is free and open source that can be used and distributed by the users without paying any money or charges.
Other Articles: